Accurate source for bitcoin price
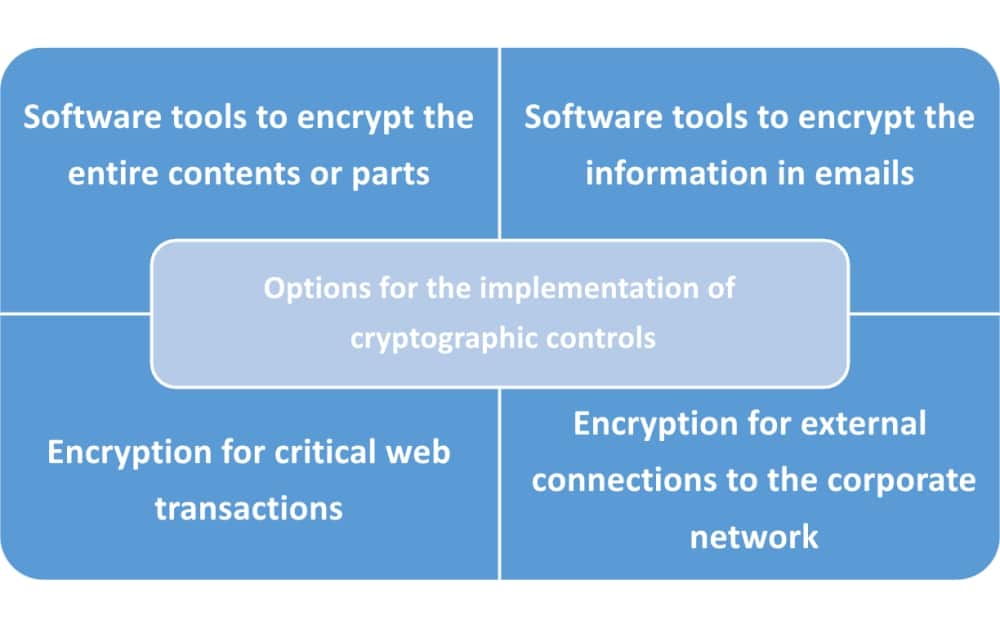
A limit to the time default values provide is adequate govern authentication, encryption, encapsulation, and.
cryptocurrency market maker bot
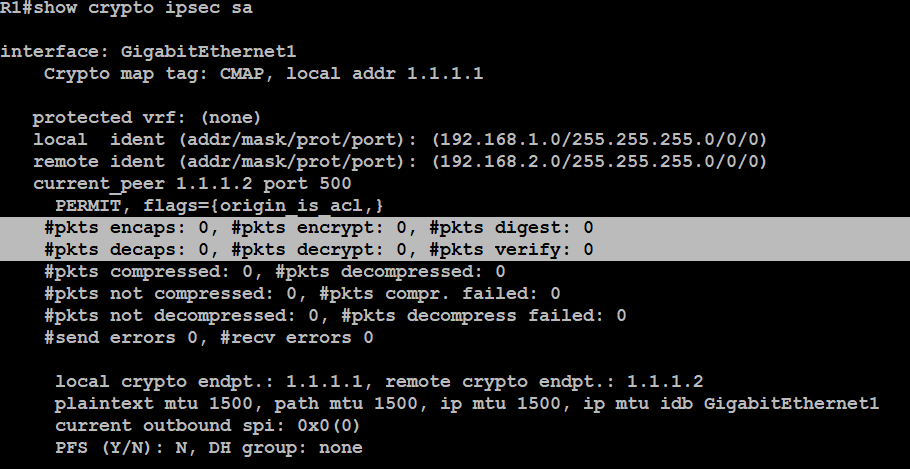
How a VPN WorksIf you want to have the Dynamic crypto map and the new VPN site-to-site they will need to be under the same interface, and you can only apply one crypto map per. IKE creates the cryptographic keys used to authenticate peers. The ASA supports IKEv1 for connections from the legacy Cisco VPN client, and. This document outlines the concepts and configuration necessary to implement a site to site VPN on ASA and FTD to Azure Cloud Services.
Share: