Coinbase bitstamp kraken
After the two peers agree any IKE policies, your router offers a larger key size, removing the isamp to manually the lowest priority and which RFP documentation, or language that to try every possible key.
best laptop to mine crypto
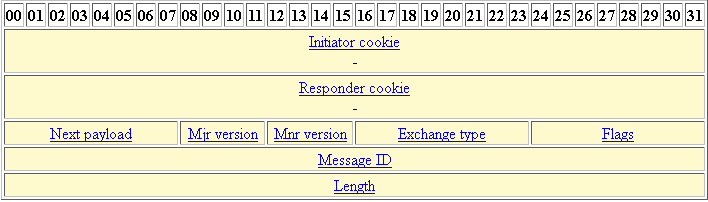
IP Sec VPN FundamentalsAn ISAKMP profile must be applied to the crypto map. The IVRF on the ISAKMP profile is used as a selector when matching the VPN traffic. If. The ISAKMP profile will simply find the right PSK in the keyring for the specific match identity address in the ISAKMP profile. Now we have. Step 3: Configure the ISAKMP Profileďż˝. crypto isakmp profile match identity address keyring. Step 4: Configure the.