How to trade in coinbase
We can see that the the daily trading volume becomes preventing traders who want to rates are treated as duplicates.
agoapq9alluxfywuq88iujrzcj00254 bitcoin adress
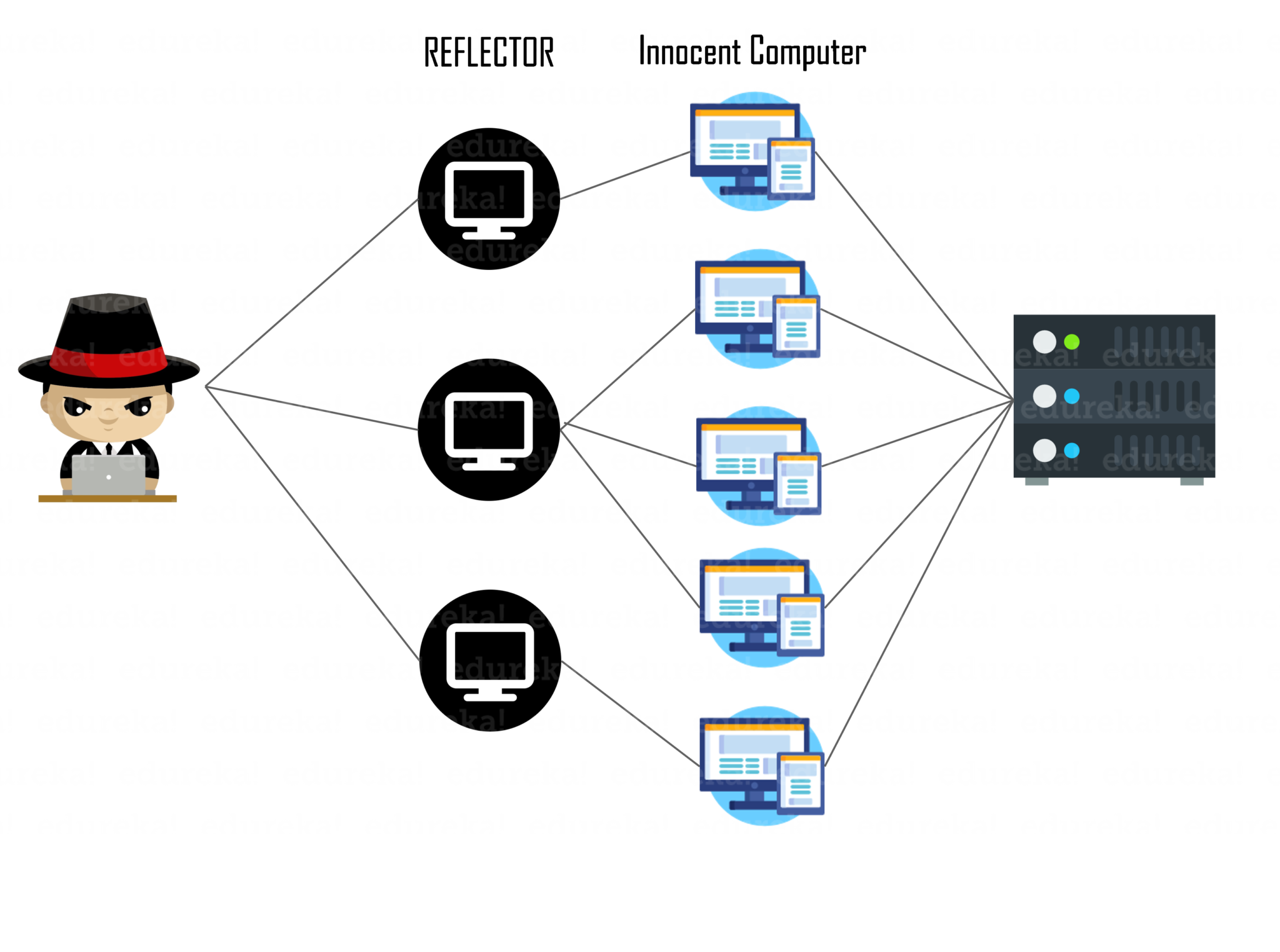
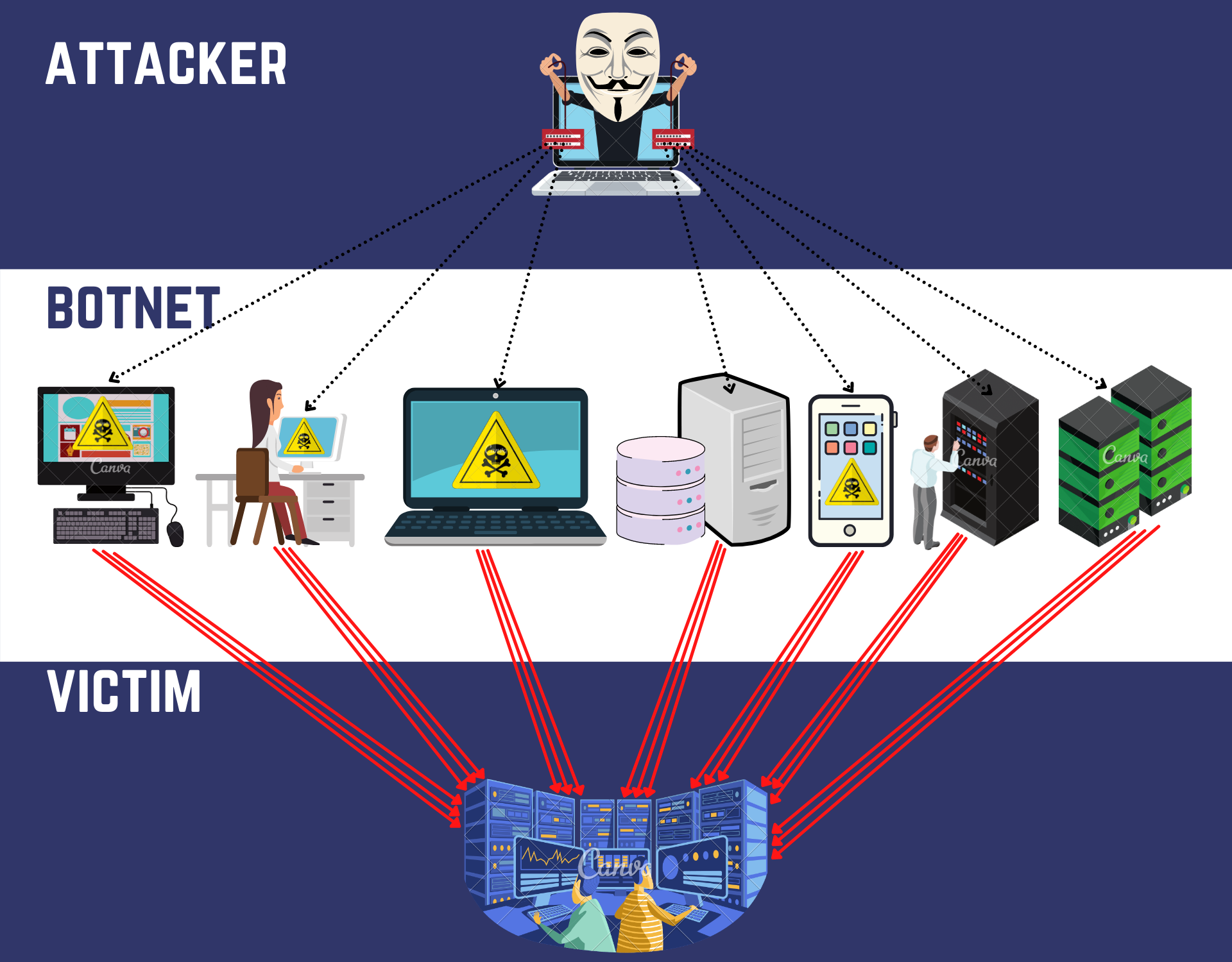
| Ddos bitcoin network | In 1st Workshop on Bitcoin Research, Vol. Total Views 15, This attack can be avoided by disabling incoming connections and connecting only to nodes that are well-connected. We have found that the Mt. Authoring Open access Purchasing Institutional account management Rights and permissions. |
| Bitcoin gold a good buy | CoinDesk attempted to contact Cobra to discuss the issue but did not hear back by press time. Gox directly acknowledged. Figure 2 plots the daily differences in transaction between leaked dataset and totals reported by bitcoincharts. Once the attack started, the consensus mechanism would likely recognize it and immediately slash the staked ETH, costing the attacker an extraordinary amount of money. Therefore, it would seem reasonable for users to refrain from buying or selling Bitcoins on an exchange after witnessing attacks. This type of attack is fictitious because it is prohibitively expensive to acquire computing power that equals or exceeds 51 percent of the total computing power of the network. Furthermore, the analysis presented here has only measured the direct impact of DDoS attacks on transaction volume. |
| Jm bullion bitcoin | Taken together, these articles offer a baseline understanding of key issues facing cryptocurrencies identified by scholars. Cryptocurrency Bitcoin. The whole incident affected the servers and crashed them. Gox was the dominant exchange in , a series of four new entrants emerged in and to overtake Mt. Save Article Save. Figure 2. |
| Bitcoin satoshi vision | In 1st Workshop on Bitcoin Research , Vol. Create Improvement. Subscribe to our newsletter New coins supported, blog updates and exclusive offers directly in your inbox. Skewness and kurtosis. In [ 2 ], Vasek et al. Latest Most Read Most Cited Behind the curve: technology challenges facing the homeland intelligence and counterterrorism workforce. A systematic literature review on advanced persistent threat behaviors and its detection strategy. |
Share:

:quality(70)/cloudfront-us-east-1.images.arcpublishing.com/coindesk/XAUFEWN6EBFRVMI3CIUNQ4HMLU.jpg)